Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
PCI Compliance Done Right with Splunk
The New Year brings with it so much to look forward to and we are happy to bring even more to be excited about: a new release for the Splunk App for PCI Compliance. Starting January 11th, version 5.1 will be Generally Available. In this blog, let's review the main benefits of the Splunk App for PCI Compliance and highlight the improvements that version 5.1 brings.
The Payment Card Industry Data Security Standard
As a CIO, you're likely familiar with the Payment Card Industry Data Security Standard (PCI DSS). But what do you know about it? PCI DSS is a set of requirements designed to protect credit and debit card data. It applies to anyone who processes, stores, or transmits payment card information.
What is PCI Compliance?
In today’s fast-moving and competitive marketplace, you can barely find any businesses and merchants that still haven’t adopted the use of credit cards for their services. More than a third of American cardholders use credit cards for their transactions on a monthly basis. With the rising prevalence of identity theft, over 1.1 billion personal records were exposed by data breaches and credit card fraud alone.
3 Steps To Remain PCI Compliant with your AWS Configuration
Becoming and staying PCI compliant both take a lot of work. Developers are often already swamped with an endless list of tasks, and adding PCI compliance can be overwhelming. Security awareness is one thing, but a set of requirements is entirely different. It means you have less freedom in how you wish to implement security in your application, and you must understand the requirements demanded by your organization.
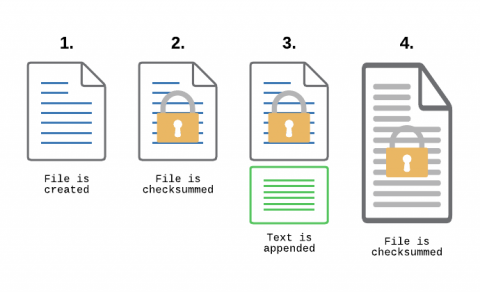
Monitoring Transaction Log Files for PCI compliance
File Integrity Monitoring, aka as FIM, is a must-have feature for anyone in charge of security. With FIM, one can detect when a critical file, such as a file that belongs to the Operating System, or a key configuration file, is changed. In most cases, configuring FIM is straightforward: If the file changes then generate an alert.
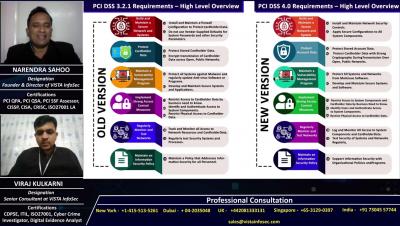
PCI DSS v4.0
2022 is the year that much of the world managed, to varying degrees of success, to get back to normal. People ramped up traveling, returned to in-person activities and many returned to the office. The pandemic changed most aspects of day-to-day life, but hackers and other bad actors generally continued making life difficult for businesses, governments, and non-profit entities.
PCI DSS Readiness Assessment
The PCI Council has set a robust framework comprising a comprehensive set of requirements for enhancing the security of payment card data. So, prior to performing the final PCI DSS Audit, most Level 1 Merchants conduct a PCI Readiness Assessment. This is to validate the effectiveness of their security implementation and the readiness for the final audit.
Defense and Development: Key points from The Complete Guide to Application Security for PCI-DSS
The increasing popularity of online payment systems results from the world’s gradual transition to a cashless and contactless digital economy — an economy, projected in a recent Huawei white paper, to be worth $23 trillion by 2025.
Key Metrics for Tracking PCI DSS Compliance in 2022
PCI DSS compliance ensures your customer’s credit card data is protected from hackers and compromise attempts. Though complying with this regulation isn’t easy, it is possible. To simplify this essential effort, we’ve compiled a checklist of the key security metrics that should be addressed to meet the compliance requirements of this critical information security standard.