From Reactive to Predictive: How to Enhance Privileged Session Security in Federal Environments
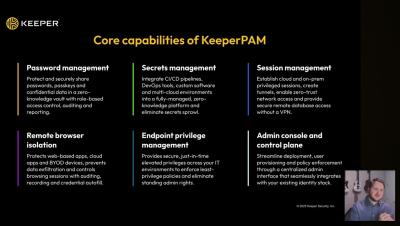
Federal agencies face a unique challenge: balancing operational efficiency with strict compliance mandates like FedRAMP, NIST and evolving zero trust requirements, all while addressing persistent cyber threats. KeeperAI, embedded in Keeper’s FedRAMP Authorized Privileged Access Manager (KeeperPAM), shifts oversight from reactive logging to real-time, predictive detection.