Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Creating a cybersecurity startup with LimaCharlie
LimaCharlie takes a radically different approach to cybersecurity, providing mature security capabilities and infrastructure in an on-demand, pay-per-use way. This opens up exciting opportunities for entrepreneurs who want to create their own cybersecurity startup using LimaCharlie.
Malicious Packages Special Report Reveals 315% Spike in Attacks
Today’s attackers aren’t just exploiting vulnerabilities — research from Malicious Packages Special Report: Attacks Move Beyond Vulnerabilities illustrates the growing threat of malicious packages. According to the report, the number of malicious packages published to npm and rubygems alone grew 315 percent from 2021 to 2022.
Australia Set to Reform Cybersecurity Rules
Passkeys vs. passwords: What are the differences?
Humans have used different forms of passwords to guard secrets for centuries. These days, we use strings of characters to access everything from garage doors to digital documents.
Introducing the Industry's First Unified, All-Software SASE Client with Integrated Netskope Endpoint SD-WAN and Intelligent SSE
There exists a drive in all of us that embraces innovation to make life easier. For IT leaders, it’s time for true innovation at the remote access edge.
Launching GitGuardian Honeytoken: your powerful ally to detect any breaches in the supply chain!
What if you could detect intrusion and code leakage early in your software supply chains? Introducing GitGuardian Honeytoken, the solution that protects your software supply chains against potential intrusions on SCM systems, CI/CD pipelines, software artifact registries, and more.
Trustwave Announces Operational Technology Security Maturity Diagnostics
Trustwave has just launched OT Security Maturity Diagnostic, which is an assessment and advisory service centered on ensuring the security of industrial automation and control systems. OT Diagnostic by Trustwave is optimized to gain insight into an organization’s current state of OT security across people, processes, and technology.
How to Find Your Source of Truth
These days it is not uncommon to see large companies trying to make do with less, which often means trying to maintain the same amount of output with less manpower. Working efficiently to improve a product while battling engineer burnout in parallel has never been more crucial.
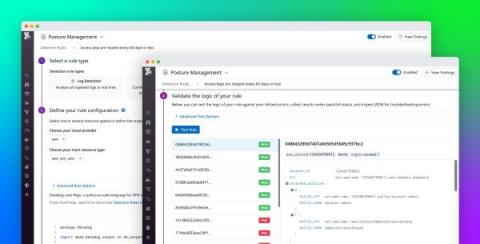
Customize rules for detecting cloud misconfigurations with Datadog Cloud Security Management
For organizations in highly regulated industries, any misconfiguration in their cloud environments can be detrimental to customer trust and privacy if overlooked. To mitigate this risk, DevOps and security engineers follow recognized compliance standards to quickly surface issues in their AWS, Azure, or Google Cloud environments. Organizations can take this work a step further by developing detection rules tailored to their unique business or security goals.