Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Application Security Requirements: Trends and Best Practices
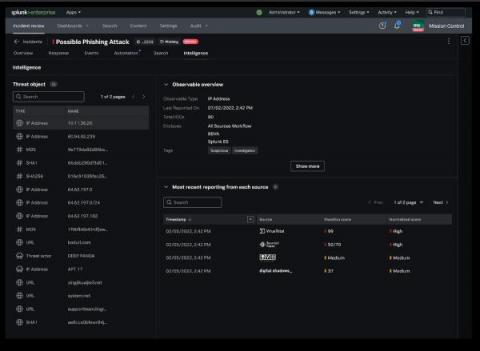
Integrated Intelligence Enrichment With Threat Intelligence Management
What Does a Password Manager Do?
A password manager stores passwords securely, generates strong passwords, identifies weak and reused passwords, generates and stores 2FA codes, and stores other sensitive data like important files. Read on to learn more about what password managers do and why investing in a password manager is worth it.
The Rekt Test: 12 Questions to Assess Your Blockchain Security
At Fireblocks, we firmly believe that industry collaboration and intelligence-sharing drives adoption of the best security practices and advances the ecosystem as a whole. This week, Fireblocks, along with fellow Web3 cybersecurity leaders, released the Rekt Test, a simple yet powerful guide for any business to test and assess the security of their blockchain application.
Multiple Junos OS Vulnerabilities Could lead to Unauthenticated Remote Code Execution
Tennessee Employees Lose Their Data to Consolidated Retirement System Breach
The Tennessee Consolidated Retirement System is a retirement and benefits program administered to many full-time employees throughout the state. If you are an employee within the state of Tennessee, there's a good chance that your data is tied up in this system and that you're relying on the program administrators to protect your personal and financial information.
Weekly Cybersecurity Recap August 18
Financial institutions and state government agencies were the main targets of hackers this week. Major organizations like Bank of America and Hospitality Staffing Solutions were hit hard resulting in huge data losses for citizens, and the states of Pennsylvania, Vermont, and Tennessee each experienced major data losses in their regulatory bodies or programs. Learn more about each of these serious data breaches and find out if your information is safe.
Prioritizing cyber resilience in response to a potential ransom payment ban
Ransomware attacks do not simply start and end with a locked computer screen and a ransom note. They unravel as intricate narratives, leaving a trail of financial wreckage, operational interruptions, and reputational damage in their wake. These attacks bear significant costs. In 2022, the average cost of a ransomware attack was a whopping $4.54 million, per IBM Security and the Ponemon Institute. And that does not include the actual ransom payment itself.
Impact of the New SEC Cyber Incident Reporting Rules on the C-Suite and Beyond
We recently hosted a compact and very engaging panel discussion about the new SEC Cyber Incident Reporting Rules due to come into effect later this year. We were fortunate to be joined by two well-known experts: In the post, we will *not* rehash what was said in the panel discussion. If you did not get to attend the live session, we invite you watch it on-demand – it’s 30 minutes well spent!