Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Mastering the Art of Trip Planning: A Comprehensive Guide
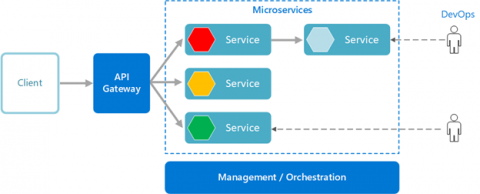
Navigating the Evolution: A Tactical Guide to Monolithic to Microservices Transformation
Major Supply Chain Cybersecurity Concerns and 7 Best Practices to Address Them
9 Steps to Protect Against the Next MOVEit/MFT Attack
By now, the facts of the recent MOVEit breach are well known (although the victim total keeps climbing), but it never hurts to be reminded that these attacks do not take place in a vacuum and threat actors are more than happy to repeatedly use the same tactics if their targets remain vulnerable. Trustwave SpiderLabs, has tracked and documented these events explaining how threat actors were found to be exploiting three vulnerabilities, including a zero-day, (CVE-2023-34362, CVE-2023-35036.
11K Bank of America Customers Lose Data to Breach
Ernst and Young is one of the leading consulting companies that helps with strategic and transactional taxes. The company offers excellent services to other major companies and handles a large amount of financial and personal data for all the customers impacted by them. This organization works with major clients like Bank of America, which is now more than 11,000 Bank of America customers were exposed in a recent data breach involving this company.
The New Network Dictionary: AvidThink Explains SASE, SD-WAN, SSE, ZTNA, MCN, and NaaS
The enterprise networking and security market has seen no end to terms and acronyms. SASE, of course, is chief among them, but let us not forget SD-WAN, SSE, ZTNA, and Multi-Cloud Networking (MCN). Then we get into specific capabilities like CASB, DLP, SWG, RBI, FWaaS, and micro-segmentation. This alphabet soup of jargon can confuse even the most diligent and capable CISOs and CIOs, especially when vendors continually redefine and reclassify each category to fit their needs.
Defender for IoT's Firmware Analysis Tool is Exceptional
One of my "pastimes," if you will, is to check out the features of various security tools. I had been curious about Microsoft's Defender for IoT's just-released Firmware Analysis feature. Essentially, I wanted to test its capabilities because, as we all know, adversaries are continuously upping their game making tools like this increasingly important when it comes to maintaining an organization's security.
Singapore Police Arrested 10 Scammers Involved in a Fraud Targeting Android Users
Read also: Chinese national charged in Australia for a $100M online investment scam, Australia busts an international card skimming syndicate, and more.
5-Step Guide on Securing Serverless Architectures in the Cloud with RASP
Serverless architecture has increased in recent years, and is anticipated to grow by nearly 25% over the next decade, According to one source, the serverless architecture market was worth over $9 billion in 2022, with its compound annual growth rate projected to increase. The market could be worth over $90 billion by 2032. This indicates the immense amount of potential that this industry carries, influenced by the increasing adoption of DevOps by organizations.