Partner-level vulnerability assessment and patch management for MSPs in Acronis RMM
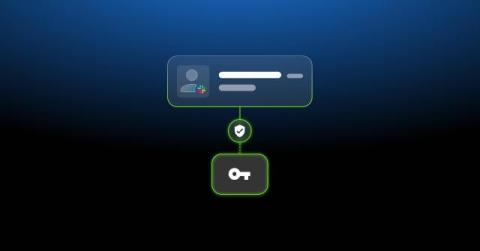
For MSPs, vulnerability assessment and patch management are challenging primarily because of scale. Every new customer adds another tenant to configure, monitor and maintain, which multiplies operational overhead and increases the risk of inconsistency. The newly released cross-tenant, partner-level vulnerability assessment and patch management in Acronis RMM is designed to break this pattern.