Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Future of Transactions: Understanding Secure Subscription Payment Systems
Unravelling the TDIR framework: Conception, evolution, and categorization
Cybersecurity is a mix of both reactive and proactive approaches. In the past, enterprises were often limited to the reactive approach. With compliance and security strategies gaining prominence, the proactive approach is also getting the spotlight. Compared to other industries, cybersecurity is highly dynamic and cybersecurity teams adopt any new technologies that can help them optimize.
19 SEO Ranking Factors That Actually Matter in 2023
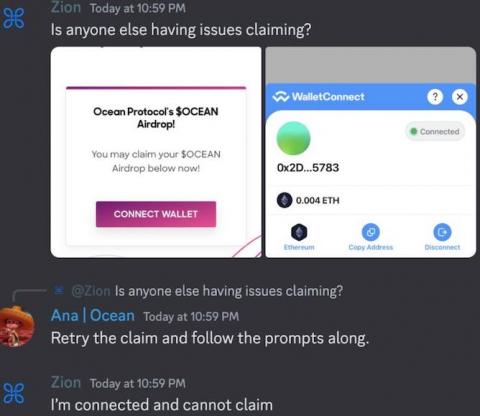
The Bookmark Trap: How Discord Admins Fell Prey to Social Engineering
Brian Krebs wrote: "A number of Discord communities focused on cryptocurrency have been hacked this past month after their administrators were tricked into running malicious Javascript code disguised as a Web browser bookmark. "According to interviews with victims, several of the attacks began with an interview request from someone posing as a reporter for a crypto-focused news outlet online.
AI Voice-Based Scams Rise as One-Third of Victims Can't Tell if the Voice is Real or Not
As audio deepfake technology continues to go mainstream as part of the evolution in AI-based tools, new data shows there are plenty of victims and they aren’t prepared for such an attack. Imagine you get a call from your child or grandchild telling you they’re in some kind of trouble, an accident, etc. and need money. And it really does sound like them. Would you help? Scammers who are making use of AI to synthesize sound-alike voices as part of vishing scam calls are hoping you will.
Russian Ransomware Cybercriminal Behind $200 Million in Damages is Sanctioned by the U.S. Government
The U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) has identified and designated Mikhail Matveev for his role in ransomware attacks back 2021. When the U.S. sanctions a country, a business, or a group, the intent is to A) confiscate any and all property owned by the designee within the U.S. or in the possession of a U.S. person, and B) add the designee to the Specially Designated Nationals and Blocked Persons (SDN) List.
php[tek] 2023 - A Community Of Communities Powering The Internet
The PHP community came together in Chicago for php 2023, sharing best practices and the latest updates from the language and frameworks that run over 77% of the internet.
Compromised Credentials: Tactics, Risks, Mitigation
AWS EC2 Vulnerability Scanning: Why Is It Needed?
The AWS cloud platform is one of the most used cloud platforms in the world. It gives companies a level of flexibility with its myriad of uses but it is not without its own challenges, namely, maintaining security.