Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Focusing On Productivity Helps Reduce Insider Risk
Many companies are concerned by the uptick in insider risk that’s come with the work-from-home boom. By one estimate, 58% of office workers work from home at least one day a week. This trend creates blind spots for companies. Managers see their employees less often, people work off network and on personal devices, and they keep schedules that don’t adhere to the previous more predictable hours.
Indicators of Compromise (IoCs): What Are They and How Do They Strengthen Cyber Defense?
What Is SecOps? Security Operations Defined in 2023
How To Use a Password Manager
How you use a password manager varies slightly depending on which password manager you have. However, they all have similar functionality. To use a password manager, you first have to set your master password, set up your multi-factor authentication methods, export and import your current passwords, download the necessary apps and create new strong passwords for each of your accounts.
Lessons from the Field, Part II: Could Better IT Strategies Help You Retain Employees?
While a number of organizations have moved back to an in-person work model, some employees are pushing back and leaving for jobs that will allow them to work from home (WFH). Having become accustomed to the advantages of a WFH model, employees have a lower tolerance for inconveniences like time and money spent on commutes, being away from loved ones for long hours, packing lunches, and having to dress for an office environment.
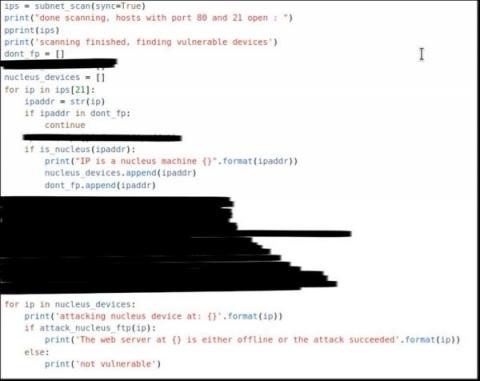
AI-Assisted Attacks Are Coming to OT and Unmanaged Devices - the Time to Prepare Is Now
Malicious code is not difficult to find these days, even for OT, IoT and other embedded and unmanaged devices. Public exploit proofs-of-concept (PoCs) for IP camera vulnerabilities are routinely used by Chinese APTs, popular building automation devices are targeted by hacktivists and unpatched routers used for Russian espionage.
Almost 2 Million Patients Exposed By Apria Healthcare Data Breach
Apria Healthcare is a healthcare equipment provider that works with more than 2 million patients annually. The company offers services in more than 280 different locations in the United States and specializes in home healthcare equipment. This organization has a significant number of employees and maintains health and personal data for employees and patients throughout the course of providing services to customers.
May Product Innovation: Updates for BIM Files, Connected Folders, and More
We are pleased to share some exciting advancements made to our platform this month. These include the introduction of folder-scoped and file type-scoped Metadata, the addition of connected folders for Desktop App Core on Mac, and significant improvements to BIM Files search and preview features. Please explore the details below for more information.
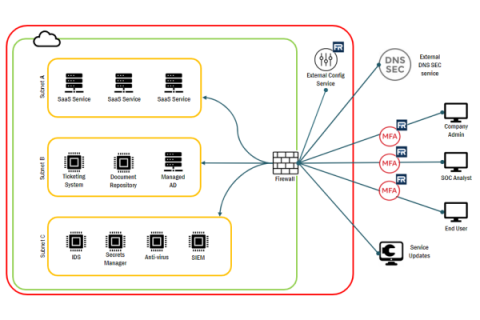
Understanding FedRAMP System Boundaries
In the ever-changing world of technology, staying secure is a top priority for many organizations. Identifying and documenting system boundaries is essential for keeping data safe and secure, but what does this mean? In this article, we’ll explore system boundaries, how to identify them, and how to generate system boundary diagrams. By the end of this guide, you’ll be well-versed in understanding system boundaries and creating diagrams that can help keep your information secure!