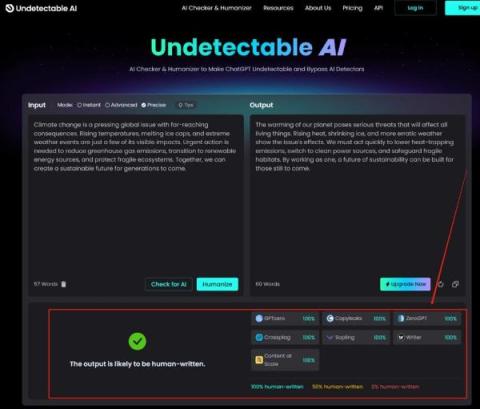
10 Best Tools to Bypass AI Detection: Ensuring Your Content Remains Undetected
In the rapidly evolving digital landscape, the advent of AI writing tools has revolutionized content creation. However, with this technology's rise, the need to bypass AI detectors has become increasingly crucial for many creators aiming to maintain the originality and human essence of their content. AI detectors are designed to identify content generated by AI, potentially leading to issues with authenticity and even penalization in certain contexts.