Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
ClearScore selects Netacea for bot protection
Egnyte Rolls Out New Governance and Compliance Tools for the Remote-work Era
From the beginning, Egnyte was architected so that your content would not have to be “boxed in” to any one single environment, but rather can flow seamlessly up, down, side to side across multiple clouds. There are good reasons for this. Sometimes it makes sense for data to be miles away, while other times it needs to be closer to where users actually are (at the edge), or offline altogether.
Session Control for SSH and Kubernetes in Teleport 4.4
Teleport 4.4 is here! The major innovation we’re introducing in this version is much improved control over interactive sessions for SSH and Kubernetes protocols. We’ll do a deeper dive into session control later, but for those who aren’t familiar with it, Teleport is an open source project. It provides access to SSH servers and Kubernetes clusters on any infrastructure, on any cloud, or any IoT device, anywhere, even behind NAT.
Announcing Netskope's Upcoming Integration for Splunk Mission Control
Today’s security operations require coordinated efforts from multiple team members, many of whom are in different roles and technology specializations. Complexity inhibits the ability to conduct time-sensitive operations such as incident response. Security engineers and the threat hunters have to be on the same page when it comes to establishing priorities and conducting investigation, across the entire detection & response lifecycle.
Exciting new features of Coralogix STA
We at Coralogix, believe that cloud security is not a “nice-to-have” feature – something that only large organizations can benefit from or are entitled to have. We believe it’s a basic need that should be solved for organizations of any shape and size. This is why we built the Coralogix Security Traffic Analyzer (STA) tool for packet sniffing and automated analysis. Today we’re announcing several new features to our security product you’ll find interesting.
Validating your IT environment, discovering browser extensions & more with EventSentry v4.2
This latest update to EventSentry improves your security posture with validation scripts, simplifies IT troubleshooting for both administrators and users, gives you visibility into installed browser extensions along with many other usability improvements in the web reports.
Veracode Streamlines AppSec Workflows for Developerswith New GitHub Action
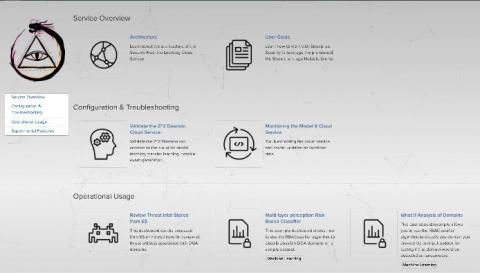
Detect Ransomware in Your Data with the Machine Learning Cloud Service
While working with customers over the years, I've noticed a pattern with questions they have around operationalizing machine learning: “How can I use Machine Learning (ML) for threat detection with my data?”, “What are the best practices around model re-training and updates?”, and “Am I going to need to hire a data scientist to support this workflow in my security operations center (SOC)?” Well, we are excited to announce that the SplunkWorks team launched a new add-
Hot off the Press: Veracode Named a 2020 Gartner Peer Insights Customers' Choice for AST
Veracode has been officially recognized by Gartner Peer Insights as a 2020 Customers’ Choice for Application Security Testing. The report includes Veracode’s aggregate score of 4.6 out of 5 stars out of 95 independent customer reviews (as of July 31, 2020), and of the reviewers, 92 percent said that they would recommend Veracode’s AST solutions. Veracode, the largest global provider of application security (AST) solutions.