Introducing the Ransomware Content Browser
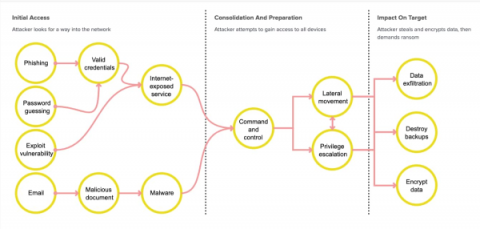
Splunk SURGe recently released a whitepaper, blog and video that outline the encryption speeds of 10 different ransomware families. The outcome of this research was that it is unlikely that a defender will be able to do anything once the encryption has started. Ransomware today is also mostly “human-operated” where many systems are sought out and compromised before any encryption activities occur and, once they do, the encryption is just too fast to meaningfully affect the damage done.