Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The State of Data Security: The Hard Truths of Data Security from Rubrik Zero Labs
Rubrik Zero Labs is excited to debut its second State of Data Security report: “The State of Data Security: The Hard Truths.” This in-depth global study is the first public use of Rubrik telemetry data to provide objective data security insights. Rubrik data is complemented by an extensive third-party study conducted by Wakefield Research, which provides a deeper look into the challenges IT and security decision-makers face, the impacts of these challenges, and possible solutions.
Automate common security tasks and stay ahead of threats with Datadog Workflows and Cloud SIEM
Detecting and remediating security threats is a constantly evolving concern for modern DevSecOps and security operations center (SOC) teams. Moreover, manually investigating and responding to vulnerabilities and threats is time-consuming, laborious, and knowledge-intensive.
Hands-on guide: How to scan and block container images to mitigate SBOM attacks
According to OpenLogic’s Open Source Adoption and Expansion in 2022 Report, the adoption of Open Source Software (OSS) across all sizes of organizations is rising with 40% of respondents stating an increase of OSS software over the previous year and 36% reporting a significant increase in OSS software usage. The increase in OSS adoption can be attributed to a number of factors including access to the latest innovations, reduction in costs and frequent product updates.
How To Detect and Prevent Insider Threats
The New UK Telecommunications Security Act: What It Means For You
Back in November 2020, the UK Telecommunications (Security) Act started its journey through the Houses of Parliament, and after many readings and much consultation it finally went live almost two years later on the 1st October 2022. At the heart of the Act was a desire to improve the security posture of the UK’s telecoms networks, infrastructure, and organisations, recognising the importance of telecommunications as part of the UK’s critical national infrastructure (CNI).
Six Key Considerations When Deploying a Web Application Firewall
The Dangers of Chatbots
It seems that Chatbots are now embedded into every digital solution at our disposal, but despite the simplicity and ease this tool provides, cyber security concerns have been raised over the AI’s ability to spread misinformation, aid hackers in developing malware and even present sensitive data leak threats.
Securing private applications with CrowdStrike Zero Trust Assessment and AWS Verified Access
AWS Verified Access (AVA), a feature of Amazon Virtual Private Cloud (VPC) networking, delivers secure, zero-trust access to private applications without a VPN by continuously evaluating each request in real time based on contextual security signals like identity, device security status and location. The service grants access based on the security policy configured for each application and then connects the users, thereby improving the security posture of the organization.
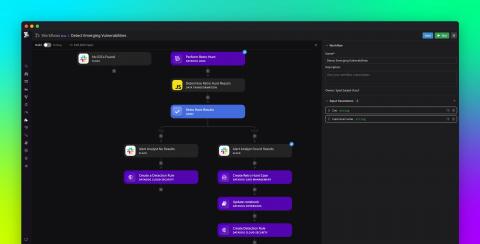
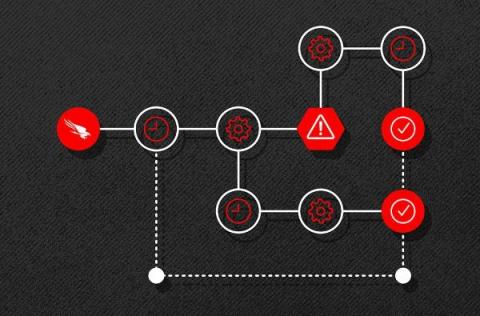
New CrowdStrike Falcon Fusion Features Refine Workflow Automation for CrowdStrike Customers
CrowdStrike Falcon® Fusion is a cloud-scale, extensible security orchestration, automation and response (SOAR) framework that’s natively integrated with the CrowdStrike Falcon® platform and available to CrowdStrike customers at no added cost.