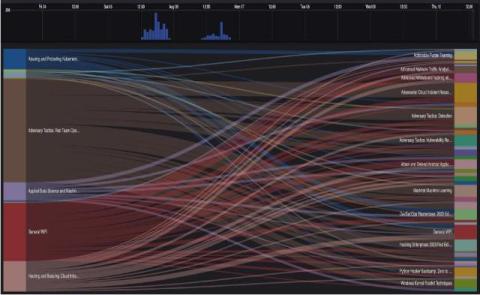
Security Misconfigurations - Detection and Automatic Remediation
Security misconfigurations can open the door to potential cyberattacks, leading to data breaches, system compromises, and other severe consequences for organizations. In modern IT environments, including cloud infrastructure and other digital platforms, these misconfiguration vulnerabilities are becoming increasingly common and complex. Preventing and addressing security misconfigurations requires a collaborative effort across DevOps, DevSecOps, and security teams.