JFrog Connect: Ready for What's Next for DevSecOps, Edge and IoT
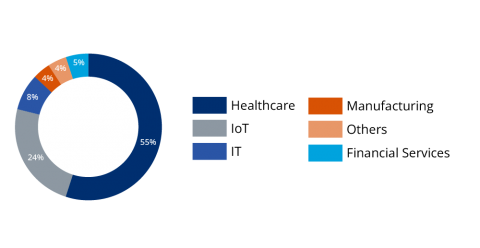
Today at swampUP, our annual DevOps conference, JFrog CTO Yoav Landman unveiled the next step toward making the Liquid Software vision of continuous, secure updates a truly universal reality. We’ve introduced JFrog Connect, a new solution designed to help developers update, manage, monitor, and secure remote Linux & Internet of Things (IoT) devices at scale.