Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
CloudCasa by Catalogic and Ondat Bring Best-of-Breed Bundled Offering for Kubernetes Storage and Data Protection
The CISO's Guide to Application Security Innovation
Threat actors operate by an ironclad rule: If it’s important to businesses, it’s important to them. And they certainly understand the crucial business role of applications. Applications are now the number one attack vector, while software supply chain attacks increased 650 percent in a year. Clearly, if you don’t already have a modern application security program, you need to build one. But how do you make sure that your program will be effective?
Getting Started With Teleport Windows Access
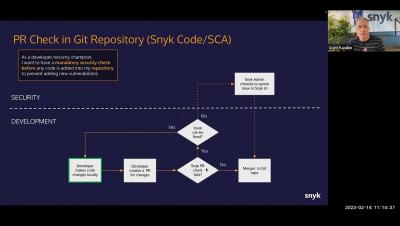
Adi Sharabani, Snyk CTO On Adapting to Change: The Future of Security in a DevSecOps World
A Day In The Life of A CISO - Prajal Kulkarni - CISO - Groww
Open Source License Management Tools: Features and Best Practices
Effectively managing the many open source licenses used in enterprise software is a complex task that requires a thorough evaluation of key features in software license management tools. After that, you need to implement the technology using several best practices. In this blog post, let’s take a brief look at both.