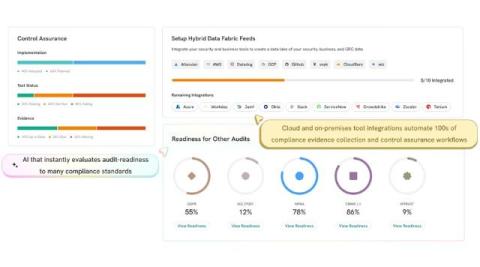
Automating compliance audits with AI: A game changer
Compliance officers and IT executives are under constant pressure in today’s rapidly evolving regulatory landscape to ensure that their organizations not only meet current regulatory mandates but also prepare for future challenges. The integration of artificial intelligence (AI) into compliance-related operations, particularly automated audits, is transforming the approach to regulatory oversight.