Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
When should a startup call the FBI
Build vs Buy for Start-ups
This is the age-old question faced by so many tech teams: do we build or buy a system we need? TL:DR, Buying can save your engineer time for building the core stack and for the fun experiments needed to determine when to shake up the core stack.
Automating Cloud Security Posture Management Remediation
When we discuss cybersecurity and the threat of cyber attacks, many may conjure up the image of skillful hackers launching their attacks by way of undiscovered vulnerabilities or using cutting-edge technology. While this may be the case for some attacks, more often than not, vulnerabilities are revealed as a result of careless configuration and inattention to detail. Doors are left open and provide opportunities for attacks.
Q2 Trends: More Cybersecurity and More Cloud
The coronavirus pandemic has forced a transformation in working practices and with it, the way MSPs manage customer cybersecurity. The possible return to the physical workplace and lingering economic uncertainties pose new challenges for tech leaders. These behavioral changes are measured in this Pulse report, which analyzes IT priorities and budgets in this area for Q2 of 2021. What do IT leaders expect the coming months to look like in terms of IT spending and priorities in their departments?
WatchGuard Cloud Honored at Cloud Computing Security Excellence Awards 2021
WatchGuard is excited to announce that once again, WatchGuard Cloud has been honored in the 2021 Cloud Computing Security Excellence Awards! This elite awards program recognizes companies that have most effectively leveraged cloud computing in their efforts to bring new, differentiated offerings to market.
Applying Least Privilege in Kubernetes II Jonathan Canada
Adopting Zero Trust and SASE as Fed and SLED Agencies Go Remote-First
The global pandemic further accelerated a trend toward remote work that was already underway, even in federal, state, and local agencies that previously resisted it. But as agencies continue to offer telework options to employees, they must also rethink their security stack to better mitigate the cybersecurity risks that remote work catalyzes. Traditional, perimeter-based approaches to security will no longer work in a cloud-first environment where data can, and is, accessed from just about anywhere.
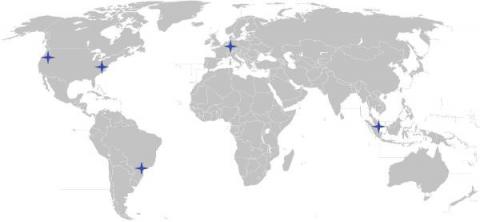
Low Latency Identity-aware Access Proxy in Multiple Regions
A multi-protocol access proxy is a powerful concept for securing access to infrastructure. But accessing numerous computing resources distributed across the globe via a single endpoint presents a latency challenge. Today we are announcing that the hosted edition of Teleport Access Plane is now available in 5 regions all over the world.