Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Shadow and Zombie APIs: How to Improve Your API Security
How to build a secure API gateway in Node.js
Microservices offer significant advantages compared to monoliths. You can scale the development more easily and have precise control over scaling infrastructure. Additionally, the ability to make many minor updates and incremental rollouts significantly reduces the time to market. Despite these benefits, microservices architecture presents a problem — the inability to access its services externally. Fortunately, an API gateway can resolve this issue.
API Security Best Practices
API Security in the fast lane
Today, an important measure for success in the tech sector is time to market. The speed at which you can launch your product and any new features can make a huge difference in meeting growing customer expectations, breaking new ground in an existing market, and standing out against your competitors.
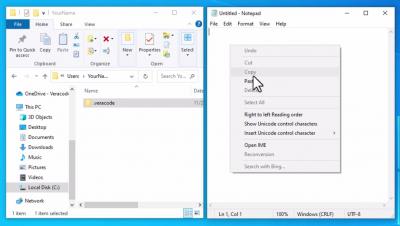
Configure the API Credentials File on Windows
An Eye for an API
If the eyes are the window to the soul, then the Application Programming Interface (API) is the window to the software. After all, an API is a way for products to communicate with each other through a documented interface, just as the eye is a human interface, communicating with the outside world (but it’s not as well-documented as to meanings).
How To Hide API Keys, Credentials and Authentication Tokens on Github
Back in 2018, GitHub celebrated 100 million open source repositories, and it has only been growing since then. How can you make sure your sensitive credentials and authentication tokens aren’t exposed to access by the public? Read this blogpost to learn how to save your API keys and other important data from being disclosed.