Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
Integrate Datadog Compliance Monitoring with your AWS Well-Architected workloads
Many of our customers rely on the Amazon Web Services (AWS) Well-Architected Framework as a guide to build safe, secure, and performant applications in the cloud. AWS offers the Well-Architected Review (WAR) Tool as a centralized way to track and trend adherence to Well-Architected best practices. It allows users to define workloads and answer a set of questions regarding operational excellence, security, reliability, performance efficiency, and cost optimization.
2021 Cybersecurity in healthcare
Breaches and cyberattacks are on the rise in the healthcare industry. The recent acceleration of digital technology and connectivity within Healthcare has led to significant patient care delivery improvements, more effective population health management, and better patient outcomes. With this increased technology and connectivity, however, comes increased exposure to cyberattacks that can impact patient care delivery, safety, and privacy.
Wishes Do Come True: Fast Development, Secure Delivery
Introducing Teleport Cloud | Access Management SaaS | Servers - Clusters - Applications
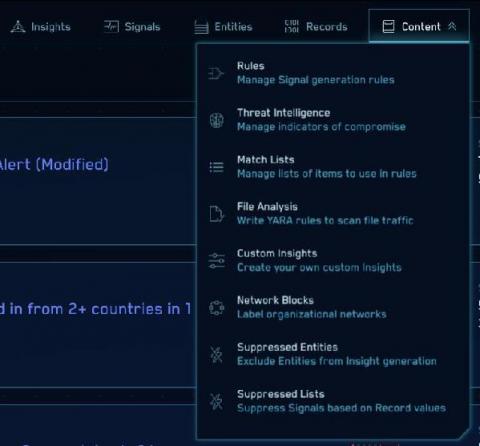
Recommendations for monitoring SolarWinds supply chain attack with Sumo Logic Cloud SIEM
How to Select a Third-Party Risk Management Framework
For many businesses, global third-party vendors have become an important source of strategic advantage and business value. Yet outsourcing is not without its risks. As reliance on third-parties continues to grow, so does the number of headline stories of regulatory action and reputational damage that arise from third-party breaches or failure. Those driving organizations need to reconsider how they approach, identify and manage third-party risk.
How to Secure Apache Tomcat 8 in 15 Steps
Apache Tomcat is the leading Java application server by market share and the world's most widely used web application server overall. Currently at version 8, the popular web server has not been without its security flaws, perhaps most famously publicized in this incident of aircraft hacking by security researcher Chris Roberts earlier this year. However, hardening Tomcat's default configuration is just plain good security sense—even if you don't plan on using it on your plane's network.
Application Security Decoded: Part 3
Learn more about Synopsys Software Integrity: https://www.synopsys.com/software-integrity.html
Subscribe: https://www.youtube.com/synopsys
Follow Synopsys on Twitter: https://twitter.com/sw_integrity
Defense in Depth: Why You Need DAST, SAST, SCA, and Pen Testing
When it comes to application security (AppSec), most experts recommend using Dynamic Application Security Testing (DAST) and Static Application Security Testing (SAST) as “complementary” approaches for robust AppSec. However, these experts rarely specify how to run them in a complementary fashion.