IT security under attack: Why are group memberships so crucial?
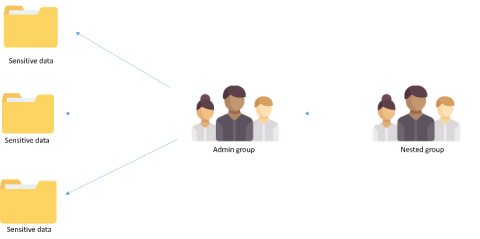
Security groups either make or break your IT security. Group memberships are responsible for administrative access in your your network and define access to other privileged resources and data on your domain. Ever wondered how a simple misconfiguration of a group membership could lead to a security incident? This blog elaborates the most common misconfiguration or security loopholes that can cause damage to the sensitive data in your network.