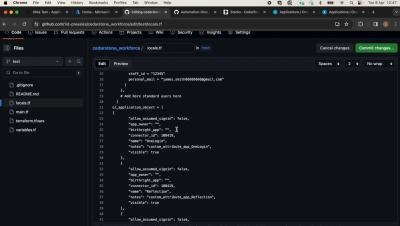
Discover your exposure to the XZ Utilities backdoor in 10 seconds or less
When high profile security events happen, it is essential for you and your team to have the information you require right at your fingertips. Using Panoptica’s powerful graph database and easy to use query engine, you are easily able to discover all the assets in all your cloud environments that could have compromised software installed.