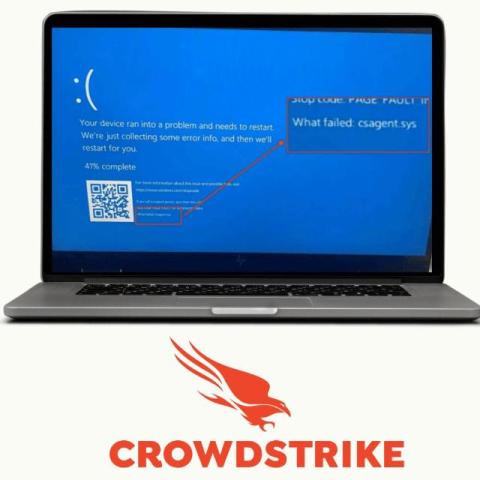
Fix CrowdStrike's BSOD with Hardening
CrowdStrike, is a prominent cybersecurity technology company that provides security services for endpoints, cloud workloads, identity, and data. They are well-known for their Falcon Sensor Software designed to protect against cyberattacks. On Thursday, July 18 2024 there was a crash on Microsoft systems related to an update in Falcon Sensor software. This update involved a single file that added extra logic for detecting bad actors.