LimaCharlie Slashes Incident Response Times With New Bi-directional Capabilities
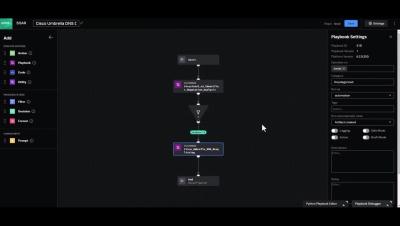
LimaCharlie introduces a new bi-directional integration platform enhancement, which allows for two-way data flows that streamline detection and response processes while eliminating reliance on third-party automation applications.