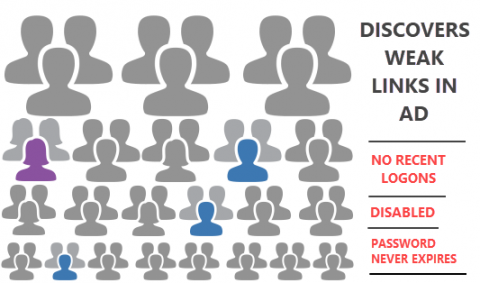
Hackers aren't confined to cyberspace anymore
Like many things in life, hackers are victims (and I use the word loosely) of stereotyping. You won’t find much stock imagery depicting hackers that doesn’t involve a hoodie, a dimly-lit room and several monitors full of scrolling binary text. And whilst that’s definitely sometimes true, it also makes several assumptions about hackers in general, which is at best misleading and at worst leaves you wide open to attack.