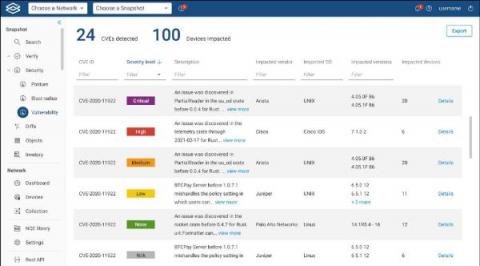
Log4Shell Peace of Mind in Minutes, Not Weeks
Discovered on December 9, 2021, the log4Shell vulnerability is one of the most talked-about vulnerabilities in computing. Because simple text can be used to take control of a device and download anything that is Internet-accessible, companies are taking it seriously. As they should – log4Shell has the maximum CVSS score of 10 (CVSS, Common Vulnerability Scoring System, is an industry-standard for ranking vulnerabilities).