Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
Dark Web monitoring and scanning explained
Shady deals often occur in darkness – criminal activities require secrecy to cloak their illicit nature. Today, you can find those dark places on the fringes of the internet, known as the Dark Web. More often than not, this is the place where cybercriminals go to monetize the data they’ve acquired as the result of a breach.
Secure Your Digital Assets - Penetration Testing Services Primer
Leveraging behavior analytics and machine learning algorithms in your PAM strategy
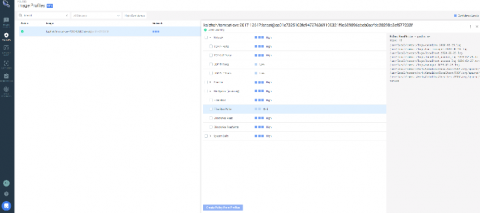
Manage AppArmor profiles in Kubernetes with kube-apparmor-manager
Discover how Kube-apparmor-manager can help you manage AppArmor profiles on Kubernetes to reduce the attack surface of your cluster. AppArmor is a Linux kernel security module that supplements the standard Linux user and group-based permissions to confine programs to a limited set of resources. AppArmor can be configured for any application to reduce its potential attack surface and provide greater in-depth defense.
Detecting CVE-2020-14386 with Falco and mitigating potential container escapes
On September 14, CVE-2020-14386 was reported as a “high” severity threat. This CVE is a kernel security vulnerability that enables an unprivileged local process to gain root access to the system. CVE-2020-14386 is a result of a bug found in the packet socket facility in the Linux kernel. It allows a bad actor to trigger a memory corruption that can be exploited to hijack data and resources and in the most severe case, completely take over the system.
Forging Better Security Outcomes with Integrated Threat Intelligence
For most companies, security and IT systems are growing in complexity, breadth of scope, and coverage, which consumes budget and staff time. The rapid breakdown of the traditional perimeter in this “new normal” world increases the challenges IT teams and remote users face on a daily basis.
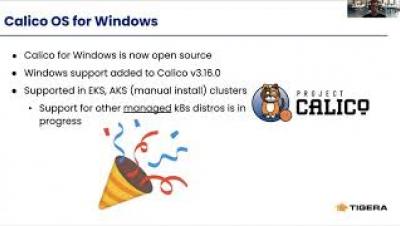
How to Secure Mixed Linux/Windows Clusters with Calico Policy
16% of Orgs Require Developers to Self-Educate on Security
Theoretical physicist Stephen Hawking was spot on when he said, “Whether you want to uncover the secrets of the universe, or you just want to pursue a career in the 21st century, basic computer programming is an essential skill to learn.” It’s no secret that programming is a thriving career path – especially with the speed of software development picking up, not slowing down.
The History of Common Vulnerabilities and Exposures (CVE)
During the late 1990s, security professionals were using information assurance tools in concert with vulnerability scanners to detect and remove vulnerabilities from the systems for which they are responsible. There’s just one problem – each security vendor has its own database with little to no crossover.