Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Endpoint Security
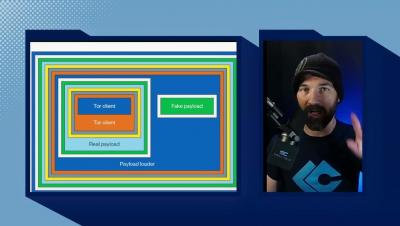
Walking Through Walls: Four Common Endpoint Tools Used to Facilitate Covert C2
Adversaries continue to find new and innovative ways to penetrate an organization’s defenses. Defenders who focus on plugging these holes can find themselves exhausted and frustrated. Hunting for adversarial defense evasion for the purpose of data exfiltration and command-and-control (C2), however, remains a good strategy. Many adversaries leverage tooling to establish C2 or to enable successful data exfiltration, all while evading an organization’s defenses.
Wi-Fi routers and access points are the most vulnerable IT devices
Today, the number and diversity of connected devices continue to grow in enterprises, no matter which sector they operate in. This has created a new challenge for organizations as they need to understand and manage the risks they are exposed to. We keep saying that the attack surface is expanding, and that's because it now spans IT, IoT, and OT for most enterprises, with the addition of IoMT in healthcare.
2022 in Review (and what's to come)
Essential endpoint security strategies for IT admins
The 443 Episode 224 - Reviving a Dead Botnet
How to make your MSP business attractive to buyers
MSPs are becoming critically important. The difficulty of finding security specialists and the high costs of managing their own security have led medium-sized companies to hire MSPs to keep their digital security up to date while they focus on their business. Growth in the MSP market means buyers are now showing interest. We are frequently seeing large and small MSPs being acquired by other larger managed services companies or private equity firms.