Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
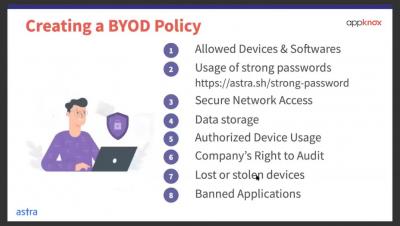
Creating a BYOD Policies
The origin of Open Policy Agent and Rego
Why the cloud-native architecture required a new policy language I recently started a new series on the Open Policy Agent (OPA) blog on why Rego, OPA’s policy language, looks and behaves the way it does. The blog post dives into the core design principles for Rego, why they’re important, and how they’ve influenced the language. I hope it will help OPA users better understand the language, so they can more easily jump into creating policy of their own.
Hardening Windows security: How to secure your organization - Part 2
We’re back with part two of our three-part blog series on living-off-the-land attacks. If you missed part one, you can read it here. In a nutshell, living-off-the-land (LOTL) refers to a type of attack where the attacker uses the tools and features that already exist in the target environment to carry out malicious activities. The concept of LOTL is not new, but LOTL and file-less attacks have been gaining popularity over the last few months.
Performing Image Scanning on Admission Controller with OPA
In this post we will talk about using image scanning on admission controller to scan your container images on-demand, right before your workloads are scheduled in the cluster. Ensuring that all the runtime workloads have been scanned and have no serious vulnerabilities is not an easy task. Let’s see how we can block any pod that doesn’t pass the scanning policies before it even runs in your cluster.
PCI Compliance for Containers and Kubernetes
Kubernetes Threat Intelligence: Detecting Domain Generation Algorithms (DGA)
The MITRE ATT&CK Framework: Privilege Escalation
Anyone who has had any experience on the offensive side of security has had fun with privilege escalation. There’s something exciting about exploiting a system to the point of getting root-level access. Since I have spent most of my time on the defensive side of the fence, the magic of escalating privileges rested in Exploiting for Privilege Escalation or stealing an administrator’s credentials.
A Zoom zero-day exploit is up for sale for $500,000
Millions of people have moved onto the Zoom video-conferencing platform as the coronavirus pandemic has forced them to work from their homes. According to Zoom’s own statistics, its daily usage has soared from approximately 10 million daily users in December to over 200 million today.
Best Practices for Building API Integrations
Modern applications aren’t built in silos. They rely on the features of other applications. This reliance can come in the form of open-source libraries, access to a wealth of data, or complex features distilled down into a consumable API. Incorporating third-party dependencies into your own project can be challenging. It comes with the benefits of faster development, and the downside of reliance. There is a relationship that happens when using a dependency.