Exploring NTFS Alternate Data Streams from a security standpoint
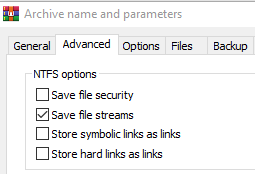
In this blog we will explore several ways that Alternate Data Streams (ADS) are abused by attackers to hide files and evade detection, defences based on them (and ways to bypass those defences!) but also how they can be used to help malware evade dynamic analysis.