Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Networks
The perfect storm: How digital transformation is reshaping security and networking
Think back to the end of 2019. Enterprises were evolving IT infrastructure at a moderate pace to reduce costs, be more competitive, and improve their ability to adapt to an increasingly digitized world. Whether migrating workloads to the cloud, virtualizing network functions, diversifying mobility, or moving applications and services closer to the edge, digital transformation was steadily evolving the business landscape.
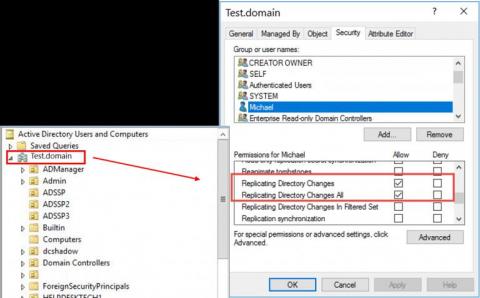
IT security under attack blog series: Instant domain persistence by registering a rogue domain controller
In this blog in the IT security under attack series, we will learn about an advanced Active Directory (AD) domain controller (DC) attack to obtain persistence in AD environments. Dubbed DCShadow, this is a late-stage kill chain attack that allows a threat actor with admin (domain or enterprise admin) credentials to leverage the replication mechanism in AD to register a rogue domain controller in order to inject backdoor changes to an AD domain.
How will comply-to-connect (C2C) help you get visibility?
How will comply-to-connect (C2C) help you with compliance assessment?
How will comply-to-connect (C2C) help you gain control?
How will comply-to-connect (C2C) provide automated orchestration of your tools?
What is Zero Trust Security and how can you enforce it?
Zero Trust Security, an alternative architecture for IT security was first introduced by Forrester and was rooted in the principle of 'never trust, always verify'. Zero trust security has come a long way since then. My message for companies that think they haven't been attacked is: You are not looking hard enough." James Snook Each enterprise and individual is at risk today given our huge dependency on the Internet.