Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Security
More Effective Security Awareness: 3 Tips for NCSAM
It’s often said that humans are the weakest link in cybersecurity. Indeed, I’d have a hard time arguing that a computer that was sealed in a box, untouched by human hand, poses much of a security risk. But a computer that is unused has no purpose. It behooves security practitioners to get smarter about how we teach people to use those machines so that both humans and computers can work together to safely accomplish greater things.
How to Comply with the NIST Cybersecurity Framework
Since NIST Cybersecurity Framework is the best solution for better prevention, detection, and response to cybersecurity incidents, various organizations have adopted it to safeguard their IT assets. The 2019 SANS OT/ICS Cybersecurity Survey spells out the NIST CSF as the number one cybersecurity framework in use today. However, it is imperative to consider that how should we comply with NIST CSF in 2020 and beyond? Here is some help!
Why endpoint telemetry is now essential to security operations
This post outlines why endpoint telemetry is now fundamental to reducing the time taken to identify and remediate security incidents.
AppSec Decoded: The security dilemma of IoT devices
In honor of National Cybersecurity Awareness Month, we’ve released a new video series that kicks off with a discussion on the future of IoT devices.
Cyber Security Planning Guide and Best Practices
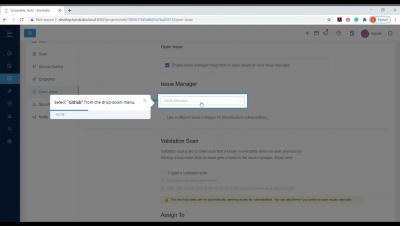
How To Open Issues On Issue Managers With Kondukto
Why Enterprise Digital Rights Management (EDRM) has an edge over Data Loss Prevention (DLP)?
WhiteSource Customer Success Story - Open Raven
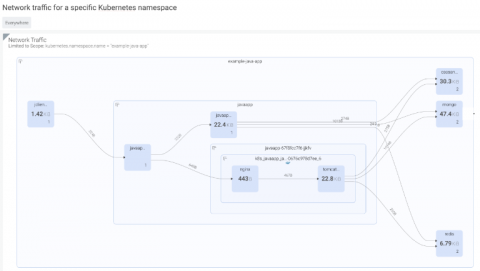
NIST 800-53 compliance for containers and Kubernetes
In this blog, we will cover the various requirements you need to meet to achieve NIST 800-53 compliance, as well as how Sysdig Secure can help you continuously validate NIST 800-53 requirements for containers and Kubernetes.