Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Security
Sysdig and IBM Embed Sysdig Secure for Container Security
What is unified endpoint management? UEM explained
The business world is undergoing its most dramatic shift yet with the adoption of digital assets and workforce decentralization representing a huge business opportunity. These changes have led to added endpoints, or devices connecting to the network, and is enabling this transformation. But managing the volumes of these diverse endpoints and geographic locations has grown in complexity.
Raising email security awareness through gamification
October was National Cyber Security Awareness Month which is an excellent opportunity to invest in a modern approach to email security awareness. Most companies and organizations conduct security awareness training annually, during onboarding, and after an adverse event. The effectiveness of periodic training varies greatly and depends on organizational culture and structure, leading to unexpected or undesired results.
Phishing awareness and phishing training explained
There is no more effective initial attack vector than phishing. With an ability to reach well-within your organization’s logical perimeter all the way down to an individual user’s Inbox with some form of malicious content, phishing has proven to be a challenge to organizations working to maintain a proper security stance. On top of this, phishing attacks have some pretty impressive accolades.
How to "winterize" and secure your eCommerce website for the holidays
With online retailers and shoppers busy focusing on the upcoming holiday shopping season, cybercriminals are on the hunt for unsuspecting victims to defraud. Don’t worry; there’s still time to beef up your eCommerce website security and get a full picture of your attack surface before Black Friday so you can #SellSafe all winter long.
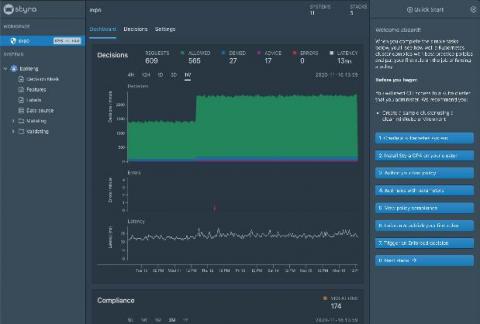
Styra Simplifies Cloud-Native Authorization with DAS Free and DAS Pro
Styra was founded with the simple premise that policy and authorization needed to be reinvented for the cloud-native environment. In order to secure and manage an exponentially more complex, containerized app development ecosystem, the team first had to build a new way to unify authorization policy at scale. The first step in achieving that was to create Open Policy Agent (OPA).
Container security on IBM Cloud
If you’re running containers and Kubernetes on IBM Cloud, you can now enable the key security workflows of Sysdig Secure as a service within your IBM Cloud deployments. This makes it easier for you to implement security tools and policies to ensure your containers and your Kubernetes environment are protected and running as intended. The new container and Kubernetes security features are integrated into IBM Cloud Monitoring with Sysdig and offered as an additional service plan.
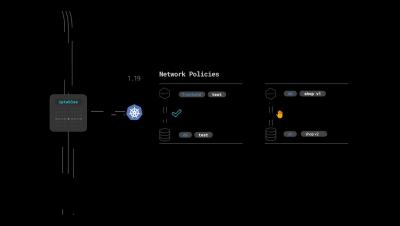
Kubernetes network policies with Sysdig
Microservices and Kubernetes have completely changed the way we reason about network security. Luckily, Kubernetes network security policies (KNP) are a native mechanism to address this issue at the correct level of abstraction. Implementing a network policy is challenging, as developers and ops need to work together to define proper rules. However, the best approach is to adopt a zero trust framework for network security using Kubernetes native controls.