Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Security
The Evolving Threat of Ransomware
Currently, ransomware is the most prominent cyber threat to businesses and individuals. Ransomware attacks are growing more prevalent as cybercriminals find new ways to profit from them. According to CyberEdge’s 2021 Cyberthreat Defense Report, 62% of organizations were victimized by ransomware in 2019—up from 56% in 2018 and 55% in 2017. This rise is arguably fueled by the dramatic increase in ransomware payments.
Obfuscate user data with Session Replay default privacy settings
Session Replay enables you to replay in a video-like format how users interact with your website to help you understand behavioral patterns and save time troubleshooting. Visibility into user sessions, however, can risk exposing sensitive data and raise privacy concerns. For example, a user session may include typing in a credit card or social security number into an input field.
New Advanced AlienApps for Akamai ETP and Akamai EAA help streamline threat management
When it comes to powerful integrations, AT&T Cybersecurity leads the way. We understand that customers want solutions that bring together visibility, response, orchestration, analytics, reporting, and more. As the attack surface continues to grow, AT&T continues to look for ways to stay ahead of threats, and one of the ways we do this is through our integrations with strategic partners in the form of new Advanced AlienApps.
Cyber Insurance: New Coverage Restrictions Expected in 2022
What are Data Processing Agreements?
No-one would lend or borrow money without expecting some form of agreement to be in place covering the term, the interest, the repayments and so on. Even lending the garden hose to a neighbour comes with an expectation of it being returned at some stage and being returned in the state that it was lent.
Weekly Cyber Security News 19/11/2021
A selection of this week’s more interesting vulnerability disclosures and cyber security news. For a daily selection see our twitter feed at #ionCube24. WordPress is wonderful – it has transformed web site development for those without a good developer and a budget. However plugins continue to remain a problem and rather than actually going through with a serious attack, a spate of faked attacks via flaky plugins are on the rise once again.
10 Essential Cyber Security Controls for Increased Resilience and Better Insurance Coverage
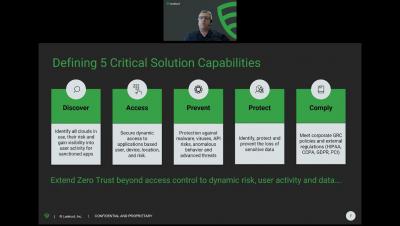
Cloud Applications: A Zero Trust Approach To Security For Healthcare
Malicious Office Documents: Multiple Ways to Deliver Payloads
Several malware families are distributed via Microsoft Office documents infected with malicious VBA code, such as Emotet, IceID, Dridex, and BazarLoader. We have also seen many techniques employed by attackers when it comes to infected documents, such as the usage of PowerShell and WMI to evade signature-based threat detection. In this blog post, we will show three additional techniques attackers use to craft malicious Office documents.