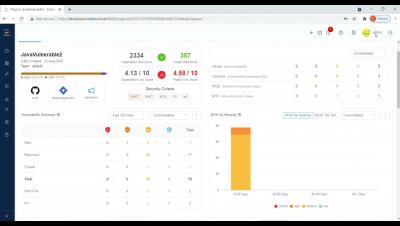
What are bots costing the financial services industry?
Netacea recently conducted a wide-ranging survey to uncover how much bots are really costing businesses. We compiled responses from 440 enterprise businesses spread across the US and UK, and have summed up our findings in an exclusive report, as well as an upcoming live webinar. Of all the sectors we surveyed, financial services was the industry most affected by API attacks, with 97% of businesses stating an API had been attacked by bots in 2020.