Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Security
Dockerfile Security Best Practices with Semgrep
The world of software development moves fast, and it's constantly evolving. Containerization technologies, especially Docker, are among today's most preferred virtualization technologies. Although Docker containers are "sufficiently" secure by default, configuration errors in a Dockerfile might lead to critical security risks or degraded system performance.
What Does the Future of Password Security Look Like?
Passwords seem seriously inadequate for security in our lives. It seems they are always getting compromised or hacked through security flaws in apps, and they never seem strong enough. Most of us will be familiar with the headaches of finding the perfect 8-character-long password, only to be told that you’ve used that one before. Even though we know we should use a different password for every secure video conference or site we create accounts for, it’s hard to remember more than one!
Cybersecurity certifications: Part of your cybersecurity journey
One of the main questions I get asked from people looking to get started in Cybersecurity is, “What certification(s) do I need?”. Who you ask and the number of people you ask will determine the number of different answers you will get back on this question. A few short years ago, there was no such thing as a cybersecurity professional. At first, people working in system administration or development were asked to take on the additional role of handling security for an organization.
How Hive becomes one of the most dangerous ransomware group
The Hive Gang is a Ransomware as a Service (RaaS) providers first identified in June 2021. Although relatively new, their aggressive tactics and ever evolving malware variants have made them one of the most successful RaaS groups of its kind. Find out how the group has risen through the ranks with their advanced ransomware kit, API based portal and negotiation services.
The LockBit Ransomware Gang to Adopt More Aggressive Strategy Involving Triple Extortion
Read also: Greece’s natural gas supplier DESFA hit with ransomware, an advanced BEC campaign targets high-ranking executives, and more.
Philippines launches new toolkit for Digitization of Identity verification
A financial technology company has announced UrGovPH, an open finance solution that will allow local governments to develop digital services across identity, finance, property, and business interaction.
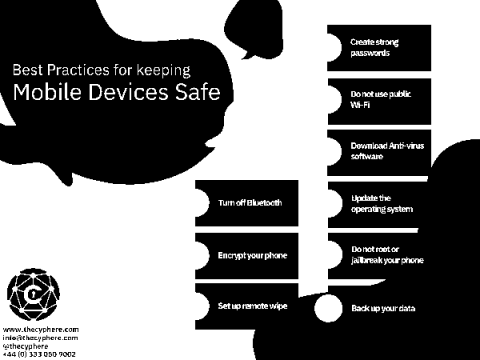
Mobile Device Security Guide: Securing your iOS and Android devices
There’s no doubt that mobile devices have become an integral part of our lives. We use them to stay connected with friends and family, get directions, check the news, and more. They’re always with us, convenient, versatile (texts, messages, calls, Internet, etc), keep us connected and loads another top reasons….in short, making our life easier! This is where mobile device security comes in, which helps protect your device from potential threats.
2022 Trustwave SpiderLabs Telemetry Report
As organizations go about their regular routine of finding and adding new technologies to help increase their overall success, each organization must keep in mind the security implications of each move, along with the fact that much of their current technology stack has to be maintained with a well-thought out and quickly implemented patching program.
SATisfying our way into remote code execution in the OPC UA industrial stack
The JFrog Security team recently competed in the Pwn2Own Miami 2022 hacking competition which focuses on Industrial Control Systems (ICS) security. One of our research targets for the competition was the Unified Automation C++-based OPC UA Server SDK. Other than the vulnerabilities we disclosed as part of the pwn2own competition, we managed to find and disclose eight additional vulnerabilities to the vendor. These vulnerabilities were fixed in the SDK in version 1.7.7.