Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Security
Breaking Down the Complexity with Cloud Through BAS
Welcome & Keynote: Increasing Attack Surface for FSIs
Into the future: what might cybersecurity look like in 2023?
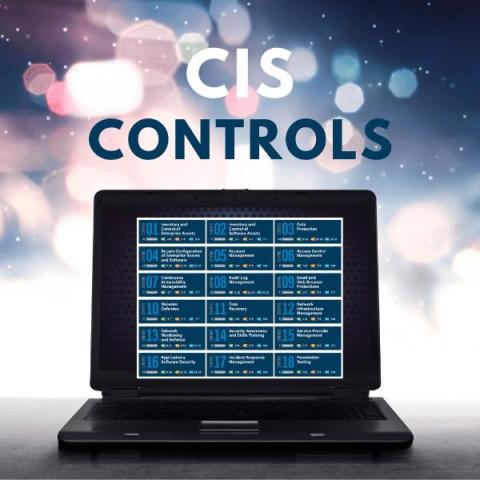
What Are CIS Benchmarks (Guide For 2023)
There are numerous CIS benchmarks which provide system administrators and other IT technicians with configuration baselines and best practices across the various levels of different CIS criteria to allow them to secure the configuration of any systems and devices they use within an organisation. Here we will provide you with a detailed overview of what CIS benchmarks and controls should mean to you, along with useful references for further reading where needed, as part of this guide.
Cybersecurity challenges facing SMBs and steps to protect them
Businesses come in many different sizes, yet, they all share one similarity; the growing need for cybersecurity in today’s ever-changing technology landscape. While large companies with robust security infrastructure and experience may ward off many aspiring cybercriminals, small to medium-sized businesses (SMBs) prove to be ideal targets.
What are CIS Benchmarks and how to use them?
Why Small Businesses Need a Password Manager
Small business owners often have to wear many hats to keep their businesses up and running. As these businesses move forward and grow in size, not only do the responsibilities build up, but so does the risk of cybercrime. For small businesses, a password manager is essential as it guarantees secure password sharing, simplifies onboarding and offboarding employees and more.
Understanding the U.S. State and Local Cybersecurity Grant Program
With over 90 thousand different state and local governments across the U.S., creating a unified approach to cybersecurity and defending all of these counties, cities, territories, states, and commonwealths is not only in each of their interests, but the national interest as well.
What were the biggest cyberattacks in 2022?
Cyberattacks consistently hit the headlines throughout the year, and they aren’t expected to slow down any time soon. While the intensity and impact change from one attack to the other, there are always a few that rank the highest in terms of size. We looked at the five biggest cyberattacks of 2022 and how they influenced users around the globe.