Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
Security and Compliance Monitoring with Forseti (Cloud Next '18)
Egnyte in Life Sciences: Bio-Techne
A.S. Roma Scores with Egnyte
Lockdown Ransomware Before it Spreads
AS Roma Football Club Scores Big with Egnyte
Modernizing Infrastructure and Creating Secure Collaboration for Their Global Organization
Business Email Attack Losses Now Top $12 Billion - FBI
The U.S. Government’s Federal Bureau of Investigation (FBI) released an open administration declaration this week cautioning that ‘business email compromise’ (BEC) scamming emails are on a dramatic increase Globally.
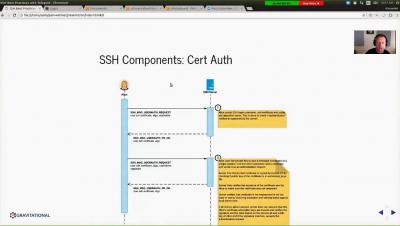
Privileged Access Management Best Practices Using SSH and Teleport
Autonomous cars: Data will drive the future
You might have not noticed it, but we are on the verge of a disruptive change in the way we humans transport ourselves. In the next five to ten years the way we think about – and take – our daily commute, our holiday vacation, trips to the market – anything that involves transport over a distance too great to walk – will dramatically change.
Questions You Should Ask Your Cloud-Based Log Management Service Provider
The log management service is often outsourced to a third-party service provider due to the complexity of the process involved in the collection of logs. When a business plans for outsourcing log management to a service provider, business requirements must be given a top-most priority. To start with, a business must identify the goals it desires to accomplish through log management. After locating the required resources, the decision-making body should select a vendor for availing its services.