Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
PCI
How to comply with PCI DSS 4.0 while juggling day-to-day tasks
In our webinar, Insights for Navigating PCI DSS 4.0 Milestones, we discuss some of the challenges organizations face as they try to comprehend the new requirements of PCI DSS 4.0.
PCI DSS Requirement 3 Summary of Changes from Version 3.2.1 to 4.0 Explained
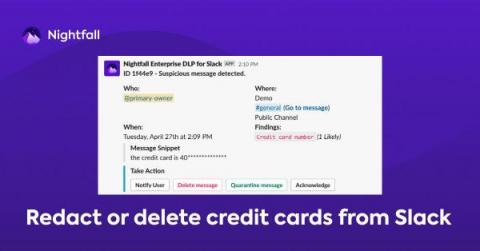
How to Prevent Credit Card Number Exposure in Slack for PCI Compliance
For many companies, a business credit card is part of the organization’s lifeblood. As such access to it must be vigilantly maintained. One potential area of risk is employees sharing credit card details in collaborative SaaS applications like Slack, where these details are at significant risk of being exposed to unauthorized parties.
Scans required for PCI DSS compliance
As a risk-based response to the continuous, and varied assaults on our systems by criminals, the PCI DSS standard requires a minimum of 20 technical scans per full year for merchants, and 21 for third-party service providers (TPSPs)
Application Programming Interface (API) testing for PCI DSS compliance
This is the fourth blog in the series focused on PCI DSS, written by an AT&T Cybersecurity consultant. See the first blog relating to IAM and PCI DSS here. See the second blog on PCI DSS reporting details to ensure when contracting quarterly CDE tests here. The third blog on network and data flow diagrams for PCI DSS compliance is here.
Explaining the PCI DSS Evolution & Transition Phase
The boon of online business and credit card transactions in the early 90s and 2000s resulted in an increasing trend of online payment fraud. Since then, securing business and online card transactions has been a growing concern for all business and payment card companies. The increasing cases of high-profile data breaches and losses from online fraud emphasized the need for urgent measures and a standardized approach to address the issue.
Guidance on network and data flow diagrams for PCI DSS compliance
This is the third blog in the series focused on PCI DSS, written by an AT&T Cybersecurity consultant. See the first blog relating to IAM and PCI DSS here. See the second blog on PCI DSS reporting details to ensure when contracting quarterly CDE tests here. PCI DSS requires that an “entity” have up to date cardholder data (CHD) flow and networking diagrams to show the networks that CHD travels over.
Candid Chats: What's the big deal about PCI DSS v4?
PCI DSS reporting details to ensure when contracting quarterly CDE tests
This is the second blog in the series focused on PCI DSS, written by an AT&T Cybersecurity consultant. See the first blog relating to IAM and PCI DSS here. There are several issues implied in the PCI DSS Standard and its associated Report on Compliance which are rarely addressed in practice. This occurs frequently on penetration and vulnerability test reports that I’ve had to assess.