Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest Videos
Active Directory Risk Review
Get instant visibility into your AD health, gaps, and any compromised credentials with a complimentary risk review.
Under the Wing: Taking on Patch Tuesdays with Falcon Spotlight
Microsoft’s Patch Tuesday is dreaded by every security team. With dozens of new patches inundating your team every month, how do you know which to prioritize? CrowdStrike combines the power of our world-class machine learning and our unparalleled intelligence to arm every customer with the insight they need to prioritize patches and take action. In this Under the Wing episode, you’ll learn how CrowdStrike enables you to protect your organization with Falcon Spotlight.
Cloud Asset Inventory and Visualization
Track your cloud asset inventory at a high level in one view and continuously monitor your cloud assets and investigate details about individual assets in the Cloud Assets table and graph. The Asset Inventory Overview shows top counts, trends, detections, and more across multiple clouds. Filter the widgets to see the info you want, and click areas in the widgets to see details in the Cloud Assets table.
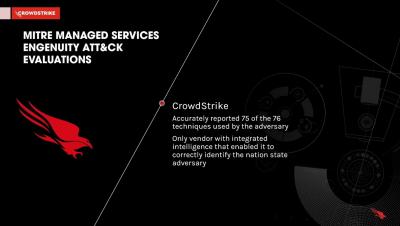
2022 MITRE ATT&CK Evaluation for Managed Services | CrowdStrike MDR Results
See how CrowdStrike Managed Detection and Response (MDR) achieved the highest detection coverage (99%) in the 2022 MITRE Engenuity ATT&CK Evaluations for Security Service Providers, accurately and conclusively reporting 75 of the 76 adversary actions and identifying the threat actor in minutes.
Under the Wing: Detecting Fileless Attacks with Advanced Memory Scanning
In 2021, over 60% of all attacks were malware free. Because malware free or fileless attacks can be carried out entirely in memory, detection can be challenging. But with new cutting-edge Advanced Memory Scanning capabilities, organizations can quickly automate high-performance scanning to detect the most advanced attacks.
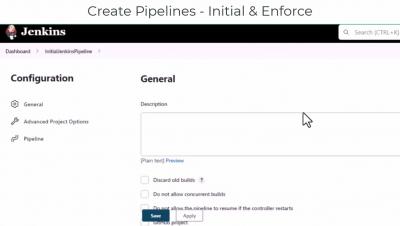
Securing your Jenkins CI/CD Container Pipeline with CrowdStrike
In any software development cycle, it is best practice to catch issues as early as possible since it both improves security and decreases the workload for both developers and security. In order to do this, CrowdStrike offers solutions for developers at build time that allow them to assess their Docker container images and review summarized report data integrated with their favorite CI/CD tools like Jenkins.
CrowdStrike Cloud Infrastructure Entitlement Management (CIEM)
Identity theft and overly permissive accounts are major challenges faced by organizations in public and hybrid cloud environments. Learn how CrowdStrike Cloud Identity and Entitlement Management (CIEM) can increase the security of your cloud infrastructure while simplifying management across clouds.
Under the Wing: Managing your External Attack Surface
Get an inside look into how CrowdStrike Falcon Surface gives you the industry's most complete adversary-driven external attack surface management (EASM) technology to stop breaches by minimizing risk from exposed assets.
Under the Wing: Stopping Identity-Based Attacks
80% of all attacks are identity-based. In this week’s episode, get an inside look into how Falcon Identity Threat Protection helps you detect identity based attacks and prevent lateral movement.