What You Need To Know About Application Security Testing Orchestration
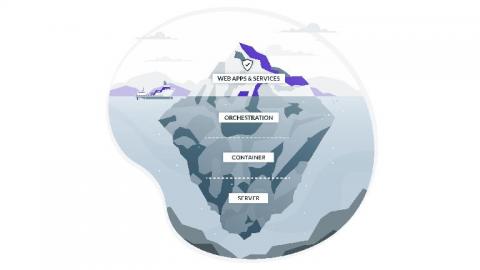
As the security threat landscape continues to evolve, choosing the best application security testing tools is just the first challenge for organizations investing in AppSec. Next, organizations need to figure out how to best orchestrate the application security testing technologies they are using in order to get the most out of them without losing valuable time. That’s where application security testing orchestration comes in.