Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
Other Ways Remote Work Has Changed Businesses
As the pandemic continues and employees are finding themselves “stuck at home” for the foreseeable future, companies are coming up with new ways to approach overall wellbeing for their employees. Things like breakroom snacks, on-site gyms, and commuting passes are less appealing and don’t make a lot of sense. So, companies are getting creative in the ways they support their employees during remote work. Here are some of our favorite examples.
Deep Dive Into PYSA Ransomware - The Monitor, Issue 18
PYSA is the most recent ransomware variant known distributed by the Mespinoza Ransomware as a Service (RaaS) gang, which has been infecting victims since 2019. Kroll has consistently observed PYSA in our incident response engagements since 2020 and has noted an increase in frequency of this variant since the second quarter of 2021. Our analysis shows PYSA is opportunistic and not restricted to one sector or geographical area.
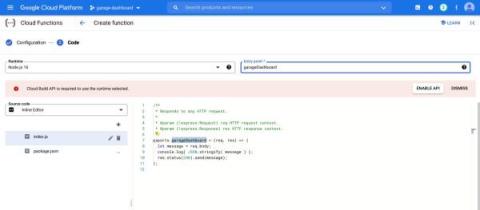
Cloud Function Dashboard with LimaCharlie
LimaCharlie provides everything you need to run modern cybersecurity operations, and it is also a great tool for builders. Our powerful web application is built using the publicly accessible API. There are no magic functions and we put the full power of the platform into the hands of those capable of wielding it. To demonstrate the kind of thing a user can easily build with LimaCharlie we have put together an interactive, embeddable dashboard.
Four cybersecurity predictions for 2022
2021 has been another challenging year for businesses, not least because of the ongoing wave of cyberattacks. Everyone is hoping for some good news in 2022, but realistically, cybercrime slowing down won’t be on the agenda. Cybersecurity and avoiding the threat of data breaches is going to be front of mind for many going into next year. We’ve spoken to two members of our leadership team who’ve shared their thoughts on four trends we’re likely to encounter in 2022.
Log4j Vulnerability CVE-2021-45105: What You Need to Know
A third Log4j2 vulnerability was disclosed the night between Dec 17 and 18 by the Apache security team, and was given the ID of CVE-2021-45105. According to the security advisory, 2.16.0, which fixed the two previous vulnerabilities, is susceptible to a DoS attack caused by a Stack-Overflow in Context Lookups in the configuration file’s layout patterns. What is this CVE about? What can you do to fix it? How does it differ from the previous CVEs?
PHP Security 101 + 1
PHP is by far the most widely used server-side programming language. Security threats surrounding PHP applications have been in the news because PHP captures over 80% of the internet with over 10 million websites built. It’s no wonder that with such a massive usage, PHP is also one of the most targeted and exploited languages, as shown in the below statistics.
CISO Interview Series: What Are Some of the Key Components to Succeeding as a CISO in Today's Business Environment?
The role of the modern CISO is more than understanding the technical side of the business. In fact, the role consists of even more than understanding the business side of the business. When I spoke with Ian Thornton-Trump, he was able to shed light on how important effective communication and team-building are to the overall success of a modern CISO. His insights can be valuable to any person currently in a CISO position and also to anyone looking to embark on the path to becoming a successful CISO.
What is Log4Shell (the Log4j vulnerability)?
Log4j, Log4j, Log4j. Let’s see you say that 10 times fast. If you can’t, then you may need to learn because Log4j is on the tips of everyone’s tongues right now. In fact, people are calling Log4j the biggest security breach since Tutar, Borat’s movie daughter, sneaked into The White House and had a lively face-to-face conversation with President Trump.
What is Log4Shell (the Log4j vulnerability)?
Log4j, Log4j, Log4j. Let’s see you say that 10 times fast. If you can’t, then you may need to learn because Log4j is on the tips of everyone’s tongues right now. In fact, people are calling Log4j the biggest security breach since Tutar, Borat’s movie daughter, sneaked into The White House and had a lively face-to-face conversation with President Trump.