Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
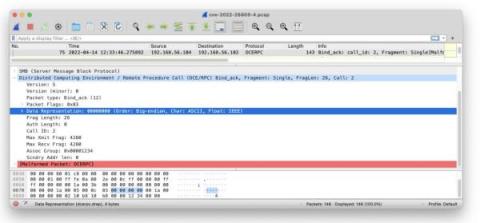
Another day, another DCE/RPC RCE
CVE-2022-26809 was patched in Microsoft’s previous Patch Tuesday (April 12) and it’s a doozy: remote code execution on affected versions of DCE/RPC hosts. The vulnerability attracted a lot of attention in the security community, both because of its severity but also because it appears to be really hard to trigger.
Monitoring Data Risks & Investigating Threats Faster With the Rubrik Data Observability Engine
Why is it that the most impressive technologies are often the ones that go unnoticed? Sometimes what makes technology impressive is precisely that it goes unnoticed, and that is the case with the Rubrik Data Observability engine. As ransomware continues to grow as a real, costly, and persistent threat to conducting business, organizations are looking for smarter and faster ways to keep data safe and recover easily in the face of cyber attacks.
Become Unstoppable with the Rubrik Data Security Command Center
From technology to healthcare to governments, ransomware is disrupting business like never before. Security teams are reevaluating their overall security posture and taking additional measures to secure their data. During this process, they are discovering that they don’t know if their organization’s data is fully secure and whether it will be available when they need it.
Stronger Cybersecurity, Thanks to the New Rubrik Security Cloud
Sad fact: cyberattacks continue to grow in volume and sophistication. Plus, ransomware doesn't hit like a bomb–it’s often more like a Trojan Horse, where many organizations don't realize they are under attack until it's too late. Despite investments in infrastructure security tools deployed at the endpoint, perimeter, and network, bad actors are still getting through to hold data for ransom.
Threat Containment: Contain the Threats, Recover the Data
A common mistake made in responding to ransomware is rushing through a recovery only to realize that the recovery point was a compromised copy of the system, and in turn, re-introduces the threat back into the environment. To make matters worse, if a replicated copy were to be recovered at a tertiary site, it might introduce malware into networks that it previously didn’t have access to and further impact business operations.
Russia-Ukraine War Raising the Awareness of Nation-State Attacks
The Russian invasion of Ukraine has heightened government and business awareness around the reality that nation-state cyber threats pose. To cover all the implications of the threat posed by nation-state actors and the groups they sponsor, we sat down with Gary De Mercurio, VP, Global Practice Lead, Trustwave SpiderLabs.
1Password 8 for Android is now in Early Access!
It’s your turn, Android folks! The newest generation of 1Password is now available in Early Access – so put on your explorer hats, help us track down those bugs, and let the feedback flow.🕵️♀️
Taking policy management to the edge (and how it's different from the cloud)
Most enterprises are well on their way towards a cloud operating model. Many have moved significant parts of their applications to one (or more) public clouds. Yet, many resources will never be destined for a central public cloud — and for good reason. We now see two factors that affect where and how many resources will ultimately be deployed (hint: it’s at the edge).