Better detections with YARA + LimaCharlie (Part 1)
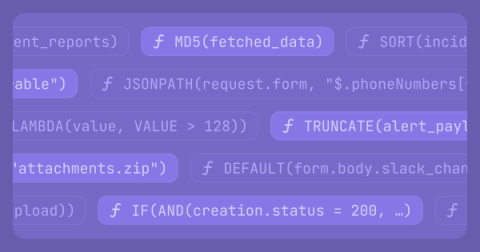
One of our core features at LimaCharlie is building an extensible platform that security teams can use to build a robust detection and response platform. One way we accomplish this is native integration with multiple types of detection engines and languages.