Spring4Shell: 12 year old vulnerability springs back to life
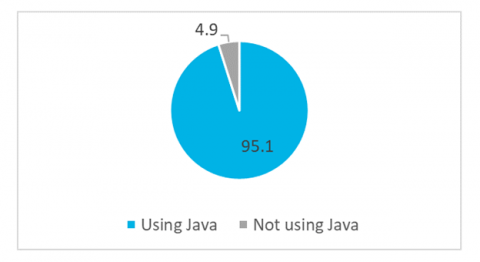
On Thursday, March 31st a patch for a widely used Java framework called the Spring Framework was given the designation CVE-2022-22965 with a CVSS Score of 9.8. That’s bad news for a lot of companies that make use of this framework for delivery of their web applications, services and APIs. This is a remote code execution (RCE) vulnerability and the ease of exploitation is partly why it has earned a 9.8 out of 10 on the CVSS Score.