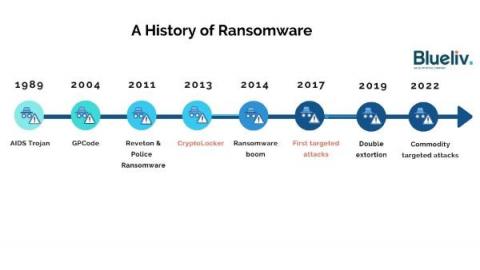
A History of Ransomware
Ransomware is the biggest cyber threat to businesses. First burst onto the scene in 1989, it has evolved significantly over the past few years from widespread attacks to highly targeted ransomware-as-a-service (RaaS) operations affecting organizations of all sizes and sectors. This article takes a look at the evolution of the ransomware ecosystem – what it looks like today, and how it has changed over time.