Mitigating Cyber Threats With Continuous Monitoring
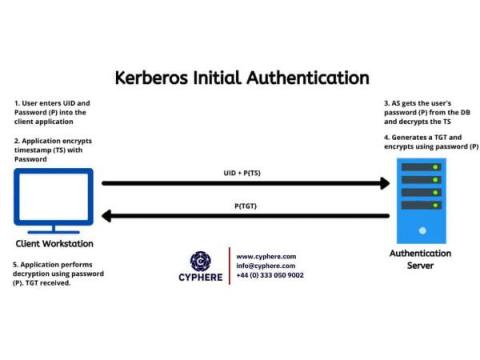
The supply chain for organizations has become increasingly susceptible to unplanned cybersecurity interruptions that negatively impact revenue, inventory, and consumer confidence. As a result, there has been an increasing focus on understanding how critical services are delivered, the reliance on third parties and fourth parties, and key risk controls that can be implemented to mitigate the risk of cyber security incidents.