Cybersecurity Awareness Month: Adding Threat to Vulnerability Management
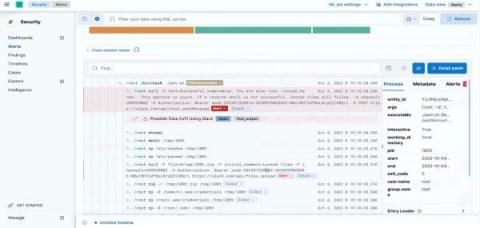
Vulnerability management can be more than just running scans and sorting by Common Vulnerability Scoring System scores! Take your program to the next level by adding a threat-based approach to vulnerability management by combining the hacker mindset with cyber threat intelligence. With so many vulnerabilities published daily, having a team knowledgeable with the latest threats can help IT teams quickly identify assets that require expedited remediation.