Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
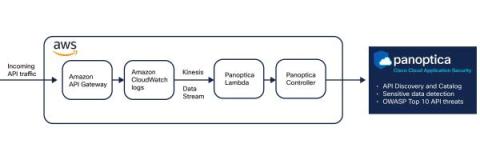
Cloud Native Security Fortified: Panoptica at AWS re:Invent 2023
Decoding CVSS 4.0: Clarified Base Metrics
How to choose the right XDR provider for your organization?
eXtended Detection and Response (XDR) technology has transformed the cybersecurity paradigm by enhancing visibility and threat detection, providing unprecedented response capabilities. It is a tool capable of monitoring the different security layers of a company, generating a single pane that unifies the detections produced in these layers.
Using RegEx for Threat Hunting (It's Not Gibberish, We Promise!)
How to perform basic digital forensics on a Windows computer
Digital forensics is a critical field in the investigation of cybercrimes, data breaches, and other digital incidents. As our reliance on computers continues to grow, the need for skilled digital forensics professionals is more crucial than ever. In this guide, we will explore the basics of performing digital forensics on a Windows computer, including key steps, tools, and techniques.
Unveiling LummaC2 stealer's novel Anti-Sandbox technique: Leveraging trigonometry for human behavior detection
The Malware-as-a-Service (MaaS) model, and its readily available scheme, remains to be the preferred method for emerging threat actors to carry out complex and lucrative cyberattacks. Information theft is a significant focus within the realm of MaaS, with a specialization in the acquisition and exfiltration of sensitive information from compromised devices, including login credentials, credit card details, and other valuable information.
What Is NIST SP 800-171 Compliance? A Guide to Protecting Your Sensitive Data
NIST SP 800-171 details requirements that all Department of Defense (DoD) contractors have been required to follow for years. The guidelines were updated in 2020, and Revision 3 was published in May 2023. Netwrix is ready to help organizations achieve, maintain and prove NIST 800-171 compliance. Below, we summarize its key requirements and share recommendations for getting started with the regulation.
Winter 2023 Product Release: What's New at Astra Security?
Free Template: MITRE ATT&CK Detection Maturity Assessment & Guide
The threat landscape has evolved rapidly in recent years due to major changes in the way organizations operate and adopt new technologies. Cloud services such as Software-as-a-Service (SaaS) and Infrastructure-as-a-Service (IaaS) have seen massive growth over the last decade. With accelerated digital transformation, increased remote working and cloud adoption, the attack surface has increased for most organizations.