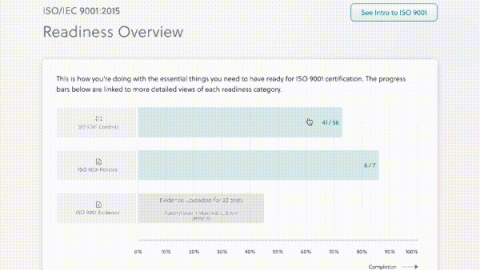
Kintent Announces Support for ISO 9001
Becoming ISO 9001 compliant can be difficult. It requires those who are seeking it to be open to change, and to be able to commit to their new Quality Management System (QMS) processes and controls. Additionally, having to continuously stay compliant with the QMS can add a lot of pressure. But… the payoff is worth it.