Essential Features Required for an Efficient DDoS Mitigation Solution
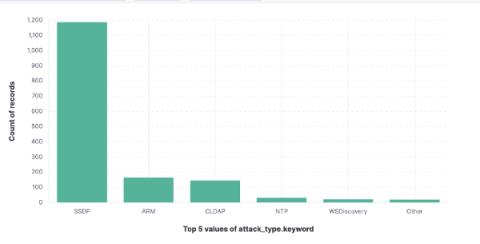
DDoS attacks affect millions of websites every day. AppTrana blocked over 4.25 million DDoS attacks on 709 websites in 2023. Indusface continues to observe a steady flow of DDoS attempts against customers: DDoS attack trends – The State of Application Security, 2023 No business is safe. How can you protect your business against DDoS? DDoS attack mitigation solution is the best weapon to protect your business against the attack.